Physical Security Risk Management

Physical Security Services
Bespoke solutions for unique risks:
- Protective Design
- Security Vulnerability Assessments (SVA)
- Threat, Vulnerability and Risk Assessments (TVRA)
- Security-By-Design (SBD)
Physical Security Risk: Understand the Threat
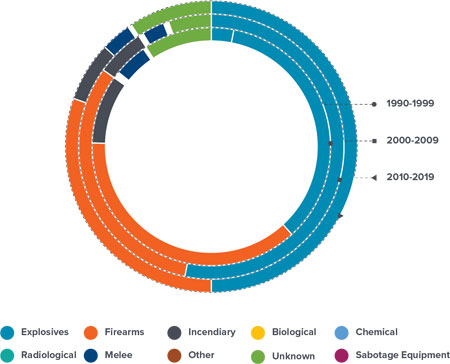
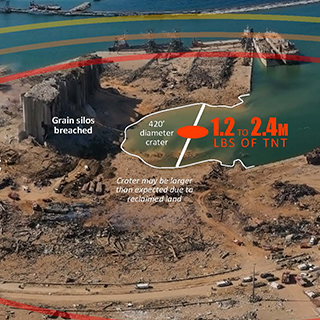
While the number of terrorism events is generally decreasing, there has been a severe increase in particular types of events. Man-made threats to commercial targets and critical infrastructure have increased exponentially, resulting in a surge in demand to protect assets from bad actors.
Understanding your exposure to physical security risks is an essential part of reducing your vulnerability to a variety of threats, including sabotage, terrorism and theft.
USE OF EXPLOSIVES
315%
Terrorist attacks using explosive devices, including incendiary, firearms and other explosives, have risen considerably.
SUPPLY CHAIN DISRUPTION
236%
Terrorist attacks on the utilities sector, including increased attacks on transportation, continue to impact the global supply chain.
ATTACKS ON FACILITIES
381%
Attacks on facilities and infrastructure have drastically increased, leaving critical operations vulnerable worldwide.
Source: Global Terrorism Database
Data: All percentage increases shown are between the decades 2000-2009 and 2010-2019
Our Approach to Physical Security Risk Management
Our extensive range of Physical Security Risk Management services provides bespoke solutions for unique problems. We work with a vast array of clients around the globe, using proven practical risk-based assessments to help them understand and reduce their risk profiles, optimize insurance expenditures, train personnel and confirm compliance with existing and impending regulatory requirements.
Memberships and Professional Certifications
-
Register of Security Engineers and Specialists (RSES)*
- Professional Engineers P.E.
- Structural Engineers S.E.
- Chartered Engineers CEng / MICE
- CP (Blast) Competent Persons
- ASIS CPP Certified Protection Professional
- ASIS PSP Physical Security Professional
*ABSG Consulting Inc. is part of ABS Group of Companies, Inc.; The UK corporate office holds registration with the Register of Security Engineers and Specialists.
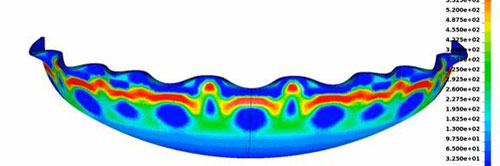
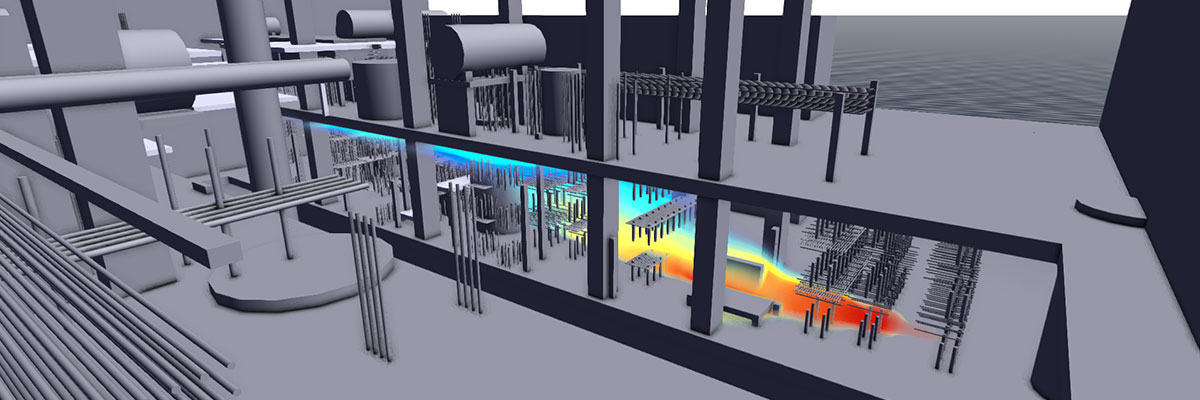
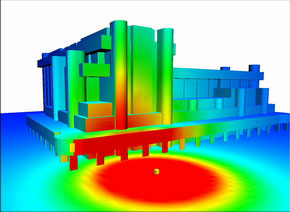
Modeling and Simulation
FACET3D
Facility Assessment and Consequence Evaluation Tool (FACET3D) is a software code that combines blast load prediction and building damage modeling into a quick running tool for engineers, security analysts and site planners. FACET3D models high explosive and vapor cloud explosions and predicts the overpressures and damage to surrounding objects. Results are displayed in a 3D graphical environment.
Other Modeling Capabilities
Our Capabilities
Protective Design
Using the built environment to protect your organization against both man-made and natural hazards is a crucial step in managing your risk. Our team of protective design engineers help clients to understand vulnerabilities to buildings and other critical infrastructure for a range of hazards and how to implement rational cost-effective mitigation strategies.
Featured Services:
- Recommendations on implementation of physical hardening measures (perimeter protection, blast analysis and design, façade strengthening, disproportionate collapse mitigation, local hardening of security command centers and other critical areas)
- Security systems evaluation and design (intrusion detection, monitoring and surveillance, access control systems, security policies and procedures, redundancy evaluations, etc.)
- Evaluation of all hazards mitigation to include Natural Hazard analysis, design, and construction management activities (seismic retrofit of buildings and structures, equipment bracing and anchoring)
- Dependency mitigation actions (emergency backup power, spare parts and supplies, cross-training of personnel, emergency response plan, business continuity plan, etc.)
View More

Security, Threat and Vulnerability Assessments
ABS Group is a leading provider of Engineering-Based Security Vulnerability Assessments (SVAs) and Threat and Vulnerability Risk Assessments (TVRA) for critical infrastructure, including water, wastewater, power (nuclear, fossil, hydro, renewable), natural gas, telecommunications, as well as oil, gas and chemical facilities.
Our Approach
- Physical SVA/TVRA assessment of critical facilities/assets for risk of various malevolent threats (theft, sabotage, assault team, product contamination, cyber-attack, attacks using explosives, etc.)
- Risk and Resilience Analyses considering threat likelihood, vulnerability and consequence
- Security system effectiveness determination for deterrence, detection, delay and response to various malevolent threats for critical facilities/assets
- Upgrade recommendations with cost estimates for physical security measures and security
- Security improvement strategies and prioritized implementation plan using risk reduction, benefit-cost analysis and other client ranking criteria
View More

Security-By-Design
Security-By-Design (SBD) considers security upfront in the development process, with security features integrated into the building design. Under the Infrastructure Protection Act (2017) in Singapore, organizations undergoing new construction must undergo an SBD review process, which requires a security and/or blast consultant to be brought on board by the Responsible Persons to prepare the security plan, which identifies the risks and vulnerabilities of a building and develops the necessary security measures to mitigate the risks.
View More

Anti-Terrorism and Force Protection
With threat levels around the world remaining significant, protecting your organization against terror events is becoming increasingly important. Our physical security consultants can support the oil, gas and chemical sectors, government entities and other organizations to understand the minimum physical security standards for their threat level.
Featured Services:
-
Window Blast Assessments
-
Vehicle Barrier Design
-
Progressive Collapse Studies
View More

Regulatory Compliance
Complying with regulatory standards is not an option but a requirement. Regulations related to security are on the rise worldwide, and the legal, financial and public relations consequences of non-compliance can be tremendous.
Regulatory Audit Support
Our team of experts provides internal and independent physical site security audit support and inspections of your security programs, as well as developing a physical security plan where needed.
NERC Compliance
Our extensive background in the electrical sector and technical expertise in risk management can help ensure that your facility is compliant with the latest North American Electric Reliability Corporation (NERC) standards and are expertly tailored to fit the needs and challenges of your specific facility.
Previous Clients Include:
- United States Department of Homeland Security (DHS)
- United States Coast Guard (USCG)
- Chemical Facilities
- Nuclear Facilities
View More

Onsite Training and Exercise Support
Our expert engineers are also leaders in world-class training and Force-on-Force Protection exercise support. We can perform onsite training and exercises with employees to help make sure your organization is prepared in the case of an emergency.
Force-On-Force Protection
- On-site rapid security vulnerability assessments of defenders and vital equipment
- Consequence predictions for air blast and fragment hazards on personnel, structures and exposed equipment
Training and Exercise Support
- Training topics include explosion basics, blast and fragments loads on structures, response prediction methods and design methods
- Security awareness training, security equipment, policies and procedures training and security incident exercises (TTX, functional, full-scale)
- Emergency response plan training, ICS, NIMS, incident response plans, emergency action plans, tabletop exercises, functional exercises, full-scale exercises and after-action reports
View More
Why ABS Group?
Site security is not just about protecting your facility from the bad guy; it's about keeping your employees and assets safe in the case of an incident. Robust security risk management plans should use the built environment, access control technology and cybersecurity to protect from intruders and prevent facility harm by ensuring your structures, operational technology (OT) and physical assets are protected.
ABS Group has decades of experience providing mechanical, civil/structural and OT cybersecurity engineering to a range of clients including the U.S. Government, nuclear facilities, and oil, gas and chemical plants. We work with our clients to understand their unique problems and find a cost-effective solution customized to their needs.